Simplify and automate
your compliance with our software GRC
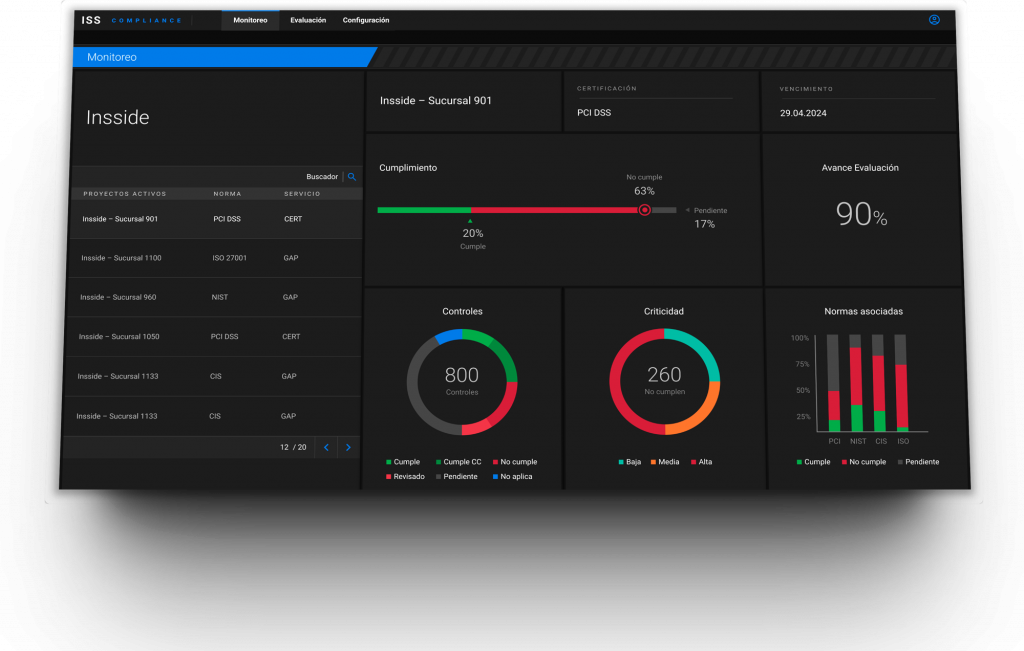
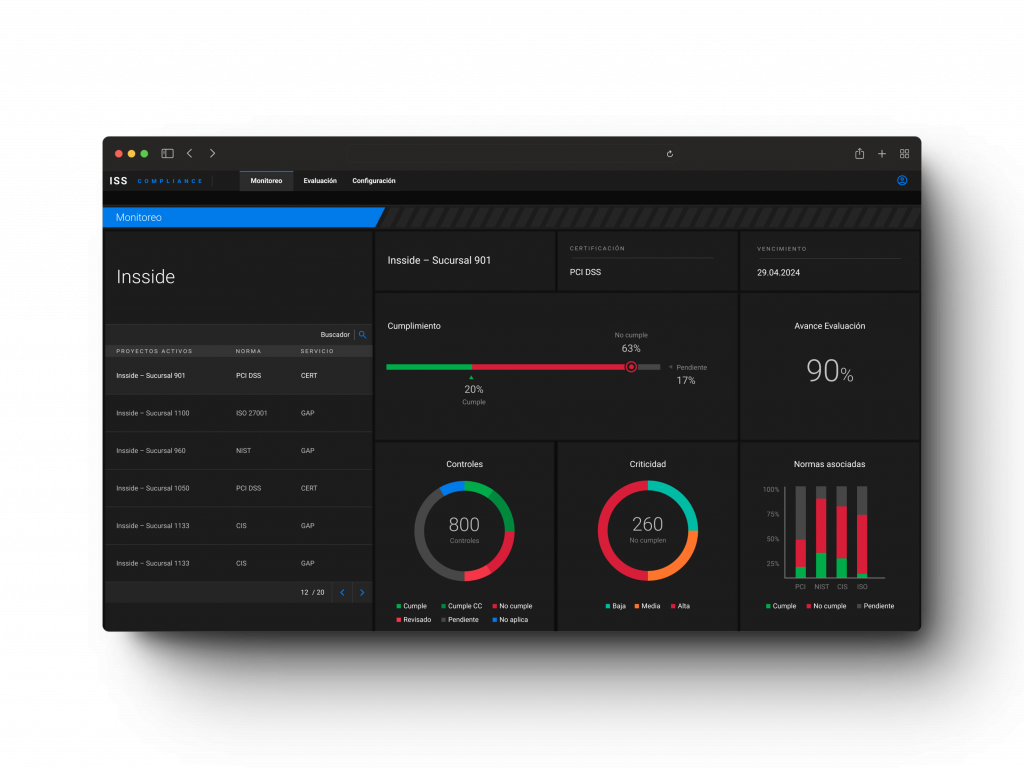
Our software GRC automates and centralizes compliance with regulations
of information security in the same platform.



Our software GRC automates and centralizes compliance with regulations
of information security in the same platform.
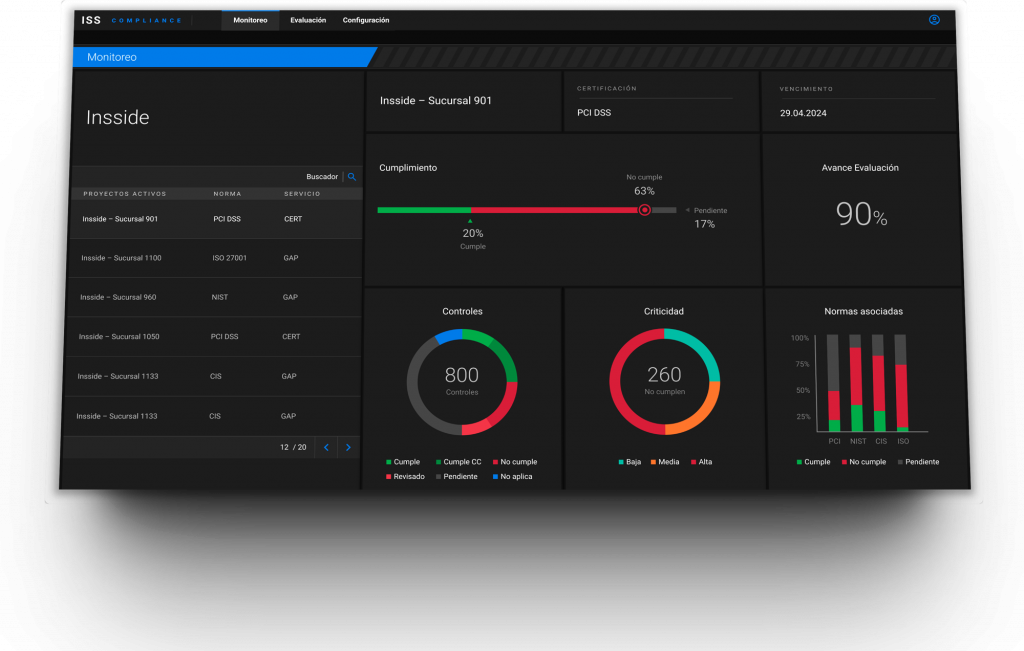



ISS automates, centralizes and provides visibility of your audit information to simplify the management.

FEATURES
Agility in the execution of cybersecurity analysis.
All the information on evaluation and monitoring of the different regulations in the same software GRC.
Speed in visualizing the level of latent risk in your organization.
Historical tracking available permanently.
Bring your own framework. Flexibility to adapt and use your own frameworks, allowing you to customize ISS according to your needs.
REVIEWS
CYBERSECURITY CHECK
At INSSIDE, Cybersecurity is a fundamental pillar. Our software GRC is backed by the professionals and leading technologies that characterize our services.

Regular evaluations to ensure the robustness and effectiveness of security protocols.
We build with security from the ground up, ensuring a robust and reliable platform.
We manage access and permissions so that each user only accesses the information and functions necessary for their role.
Implementation of end-to-end encryption to safeguard information from unauthorized third parties.
A software GRC (Governance, Risk, and Compliance) is a comprehensive platform that consolidates risk management and regulatory compliance into a single solution. It offers an integrated approach to tackle security challenges, ensuring organizations can operate efficiently and meet regulatory requirements.
By implementing GRC software, processes related to regulatory compliance, risk management, and governance are centralized, increasing efficiency by reducing administrative burdens and allowing teams to focus on strategic activities. Effective management translates to a decrease in potential fines and regulatory penalties.
Document management within ISS is facilitated through hyperlinks. Creating a hyperlink establishes a connection between ISS functionalities and the document or folder containing evidence related to compliance. This ensures that control over the information always remains in the hands of the software user.